Malware
Sandbox
System
Cyber Security Group Laboratory (SandBox system).
Your next favorite tool in your cybercrime toolbox.
Analyze files and web pages to detect viruses, Trojans and all kinds of malware.
Detect
the
Unknown
CSG Laboratory is a high-end malware analysis framework with a very agile architecture for analyzing files and Web pages to detect viruses, trojans and all kinds of malicious programs.
Unlike most well-known services, CSG Laboratory is a fully functional SandBox system with code analysis by the method of syntactic analysis, combining the analysis of static and dynamic data using various modern algorithms, which significantly increases the efficiency of detecting dangerous code.
Our Sandbox system is designed with a unique architecture, scalability and performance in mind from the beginning. Sandbox can scale up to half a million analyses per day, a rate that is hard to find in the industry.
CSG Sandbox is an advanced and automated malware analysis system with great features. Here are just a few of them:
-
01
Intuitive interface
We strive to make malware analysis easy and convenient for users of all levels. Thanks to our sandbox interface, almost anyone can start using the service right away.
-
03
Interactive analytics
Send a suspicious file to the sandbox and run an automatic or real-time analysis. Everything under your control thanks to the ability to run different scripts, reboot the system and install many programs.
-
05
High speed of work
You can get initial results almost immediately after starting a task. Often it only takes a few minutes to complete a task.
-
07
Work with API
Trace API calls and general behavior of the file and distill this into high level information and signatures.
-
09
Routing monitoring
Dump and analyze network traffic, even if it is encrypted with SSL/TLS. Built-in a native network routing support to drop all traffic or route it through InetSIM, network interface, or VPN.
-
02
Work with memory
Perform advanced memory analysis of the infected virtualized system through Volatility as well as on a process memory granularity using YARA.
-
04
Mitre ATT&CK mapping
Structural understanding of attacks is very important for threat security analysis. Our malware analysis service makes understanding understanding how the attack occurred and what methods were used.
-
06
Extensive malicious database
We constantly analyze many malware samples, which gets us access to up-to-date data and hashes from all over the world, almost instantly.
-
08
Reduced equipment costs
Our service allows launching analysis on any device and from absolutely anywhere as long as there is internet connection. Users don’t have to buy additional servers, software or hardware.
-
10
And Also...
Large number of uploads / Various pre-installed software presets / Running parallel analysis / Ability to recursively track processes, and much more.
Malware is
Platform-
Agnostic
CSG Laboratory performs automatic and interactive malware analysis in the most popular virtual environments Windows 7 and 10 (32 and 64-bit versions), Linux, Android and MacOS.
The modern sandbox engine allows to automate the analysis of more than 150 types of different malicious files (executable files, databases, office documents, pdf files, emails, etc.), file archives (ZIP-archive size should not exceed 100 MB and must include a start file), as well as malicious web pages.
Sandbox Virtual Machines (VM) launch instantly, and malware analysis unfolds right in front of your eyes.
Just as you would do it on your computer, but in a more convenient and secure way, with a variety of monitoring features.
You can easily add any suspicious file, archive or URL for checking it for malicious code. The sandbox will launch it in a real but isolated VirtualBox environment and analyze its further "behavior". Based on the detailed analysis, in just a few minutes CSG Laboratory will provide a detailed report on the actions of the observed "object" and give a conclusion about its safety or maliciousness.
-
The service shows many aspects of testing, such as:
- creation of new processes;
- potentially suspicious or malicious files;
- URLs as well as registry activity;
- network requests;
- ... and much more in real-time, allowing to make conclusions and adjustments during the task execution without having to wait for the final report.
-
CSG Laboratory offers a wide range of integrations including:
- VirusTotal and OPSWAT Metadefender (online and on-site);
- SIEM systems (e.g. HP ArcSight);
- NSRL (Whitelist);
- Thug honeyclient (e.g. URL exploit analysis);
- Suricata (ETOpen/ETPro rules);
- TOR (avoid e.g. external IP fingerprinting);
- Phantom.
We strive to make malware analysis simple and straightforward for users of all levels.
Our product is very flexible and easy to use. Due to its compact size and organizational structure, we can quickly adapt our solutions to the needs of the customer. So, even if something isn’t possible out of the box, we make it work.
After passing the test, users receive a detailed report about the system with the ability to filter by: IP, URL, domain and checksum, a specific file type, fuzzy hash, #hashtag, shared artifact and so on, search for YARA reports.
Report formats include XML, CSV, MAEC (4.1), OpenIOC (1.1), PDF, PNG, JPG, MISP XML and JSON for automatic post-processing, and HTML offline report without external references.
Years of experience come together in our smart sandbox.
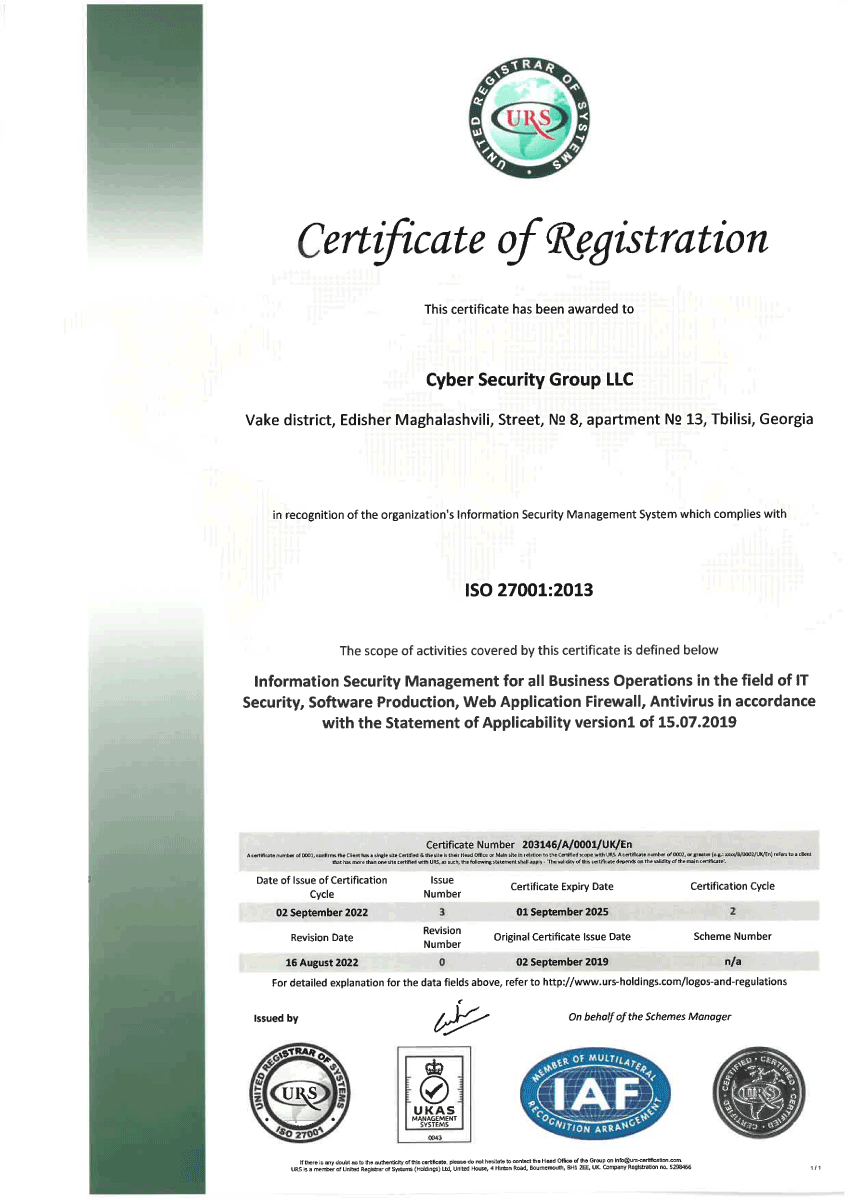
- Georgia, Tbilisi
- E. Magalashvili #8
- Contact Number: +995 557 000 342
- E-mail: [email protected]
Best
Security Checker
Solution
Malware analysis system, easy to use and customize.
Get a clear view of the critical analysis results.